Latest Attack on Android Known As “Spearphone Attack”
By Prempal Singh
“Spearphone Attack ” The New Attack, Lets Android Apps Capture Loudspeaker Data Without Any Privileges
Research revealing how more than 1300 Android apps are collecting sensitive data even when users have explicitly denied the required permissions. Primarily observed by the researcher that how developers abuse multiple procedures around to collect location data, phone identifiers, and MAC addresses of their users by exploiting both covert and side channels.
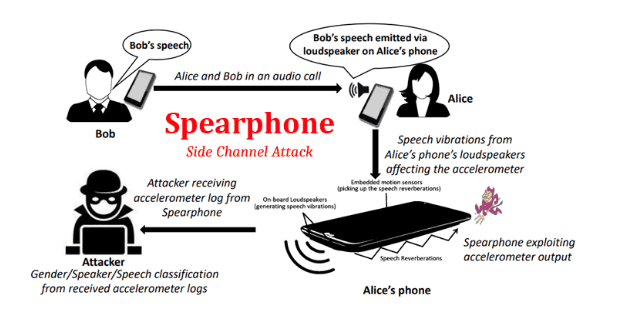
Now, a separate team of cybersecurity researchers has successfully demonstrated a new side-channel attack that could allow malicious apps to eavesdrop on the voice coming out of your smartphone’s loudspeakers without requiring any device permission.
Spearphone, a newly exhibited attack that takes advantage of a hardware-based motion sensor, called an accelerometer, which is inbuilt in most of the android devices and can be unrestrictedly accessed by any app installed on a device even without privilege. An accelerometer is a motion sensor that allows apps to monitor the movement of a device, such as tilt, shake, rotation, or swing, by measuring the time rate of change of velocity with respect to direction or magnitude.
Since the inbuilt loudspeaker of a smartphone and embedded motion sensors are placed on the same surface, it produces surface-borne and aerial speech reverberations in the body of the smartphone when loudspeaker mode is enabled.
According to the researchers, the Spearphone attack can be used to learn about the contents of the audio played by the victim—selected from the device gallery over the Internet, or voice notes which are received over the instant messaging applications like WhatsApp.
Researchers also experiment with the attack against smart voice assistants of the android devices, including Google Assistant and Samsung Bixby, and successfully captured the output results to a user query over the loudspeaker of the phone.
Besides this, Spearphone attack can also be used to simply determine some other user’s speech characteristics, including gender classification, with over 90% accuracy, and speaker identification, with over 80% accuracy.