Latest App that detects hidden Bluetooth Card Skimmers at Petrol Pumps
By Prempal Singh
In recent years Skimming attacks has increased a lot and Law enforcement agencies have reported many cases of petrol pumps where cybercriminals have installed Bluetooth card skimmers across the nation.
The media has reported several recent crimes surrounding credit card skimmers, some cases are:-
- Petrol pump skimmers found at Boerne stations.
- Fuel Station Credit Card Skimmer Found at a 7-Eleven in Pinellas County.
- Card skimmer found at the Fuel station of West Palm Beach.
- Petrol pump Credit Card Skimmers are Found at Bay Area Stations.
Basically, Bluetooth credit card skimmer is a small device designed to quietly capture payment card information, like credit card holder’s card no, full name and expiration date, which nearly thieves and then retrieve the data or information wirelessly over a Bluetooth connection.
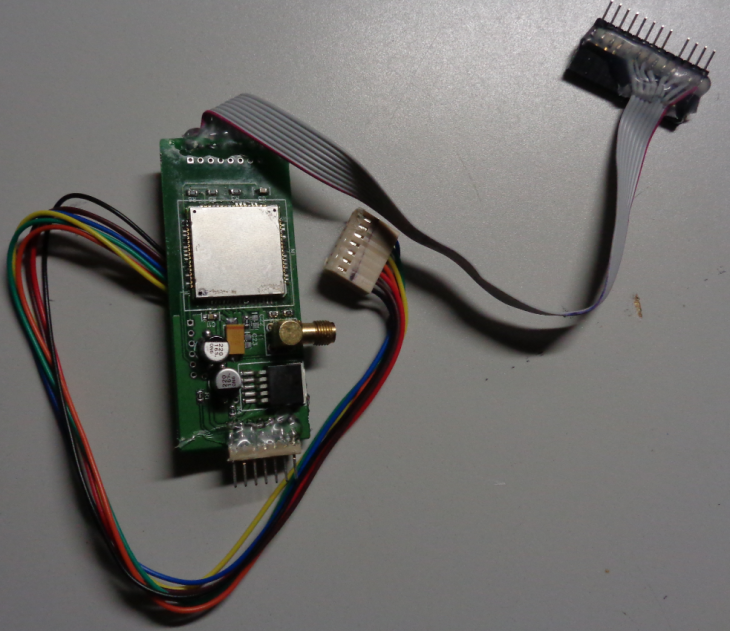
These devices are designed to blend in seamlessly with the machines they are placed on, so sometimes it’s really difficult to spot them, even if you are using your eyes, fingers and your common sense.
Few year’s back Bank ATMs are the main target for Skimmers, but in recent years attackers have started targeting fuel stations because it’s easier for them to pull off the crime in these areas.
But there is great news – it’s time to say goodbye to credit card skimmers because a team of cybersecurity researchers at the University of California San Diego and the University of lllinois has developed a new mobile app that can wirelessly, quickly and accurately detect card skimmers installed by criminals on bank ATMs and gas stations.
Bluetana, the smartphone app works by scanning all nearby Bluetooth devices – both Classic and Bluetooth Low Energy (BLE) – it’s scan after every 5 seconds using Android’s Bluetooth API and if it detected a potential skimmer, the app indicates it to the user by highlighting the device record in Red.
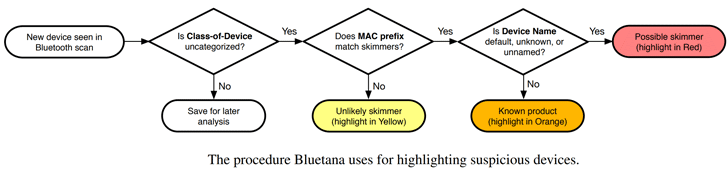
This whole process is possible because Bluetana uses an algorithm to differentiate credit card skimmers from all other common Bluetooth devices, like sensors, smartphones or vehicle tracking hardware that appear in the Bluetooth scans.
How Does This App work?
As shown in the above figure, the app differentiates devices in the following procedure:
- If the class-of-device is uncategorized, Bluetana saves its data for later analysis.
- It then matches the device’s MAC prefix against a list of prefixes used in skimming devices recovered by law enforcement agencies.
- If the device has a MAC that is not in the list, it is not likely to be a skimmer, and the app highlights the record Yellow.
- If the device MAC is in the list, but the “Device Name” matches a common product, it is unlikely to be a skimmer and the record’s highlights in Orange.
- If a device MAC prefix matches, Class-of-Device is categorized and Device Name is not common, it indicates the device is likely to be a skimmer, and Bluetana highlights the record in Red.
Researchers said that they were even surprised that their Bluetana app was able to detect so many skimmers that had not been discovered by other detection methods.
According to the study of the Researchers, Bluetana takes just 3 seconds on average to detect any card skimmer – far less than the time taken by other detection methods.Law enforcement agenciesAccording to the study of the Researchers, Bluetana takes just 3 seconds on average to detect any card skimmer – far less than the time taken by other detection methods.
For the time being, the app is only available to official gas pump inspectors in several states of the U.S and are not expected to go mainstream for consumers anytime soon, said by the Researchers.