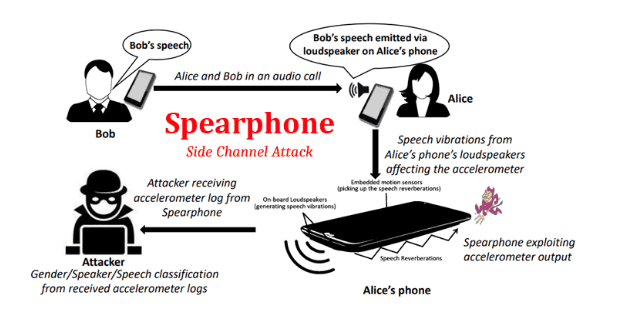
Latest Attack on Android Known As “Spearphone Attack”
By Prempal Singh
“Spearphone Attack ” The New Attack, Lets Android Apps Capture Loudspeaker Data Without Any Privileges Research revealing how more than 1300 Android apps are collecting sensitive data even when users have explicitly denied the required permissions. Primarily observed by the researcher that how developers abuse multiple procedures around to collect location data, phone identifiers, and […]