[Tutorial]: Network Attacks Using Zarp
By Prempal Singh
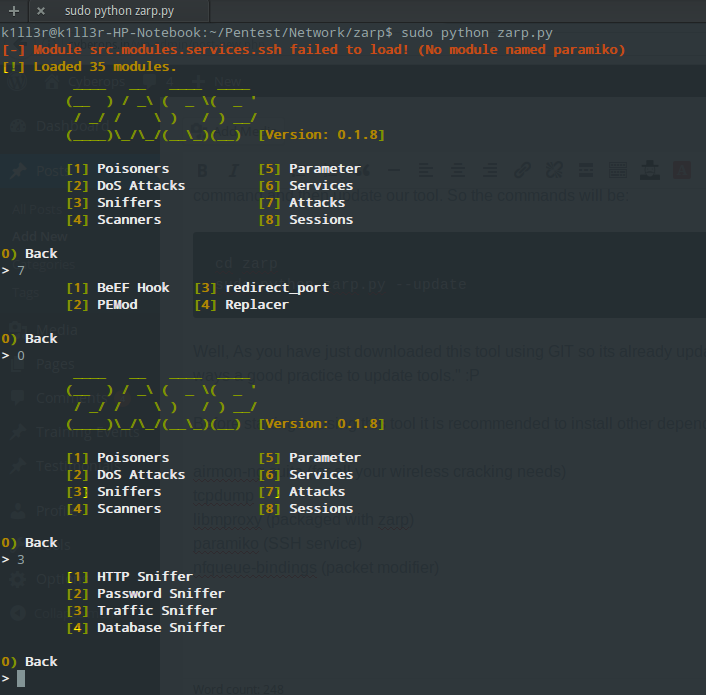
Hey guys..!!! Network Security is a field where penetration testers are paid to test organization’s Network Infrastructure’s security against different type of Cyber attacks. Having options of penetration testing tools is always a good thing. We can test any network’s security using different-different tools. From that list of penetration testing tools, we are going to introduce […]