Smart and Easy Ways to Protect Your Digital Life
By Prempal Singh
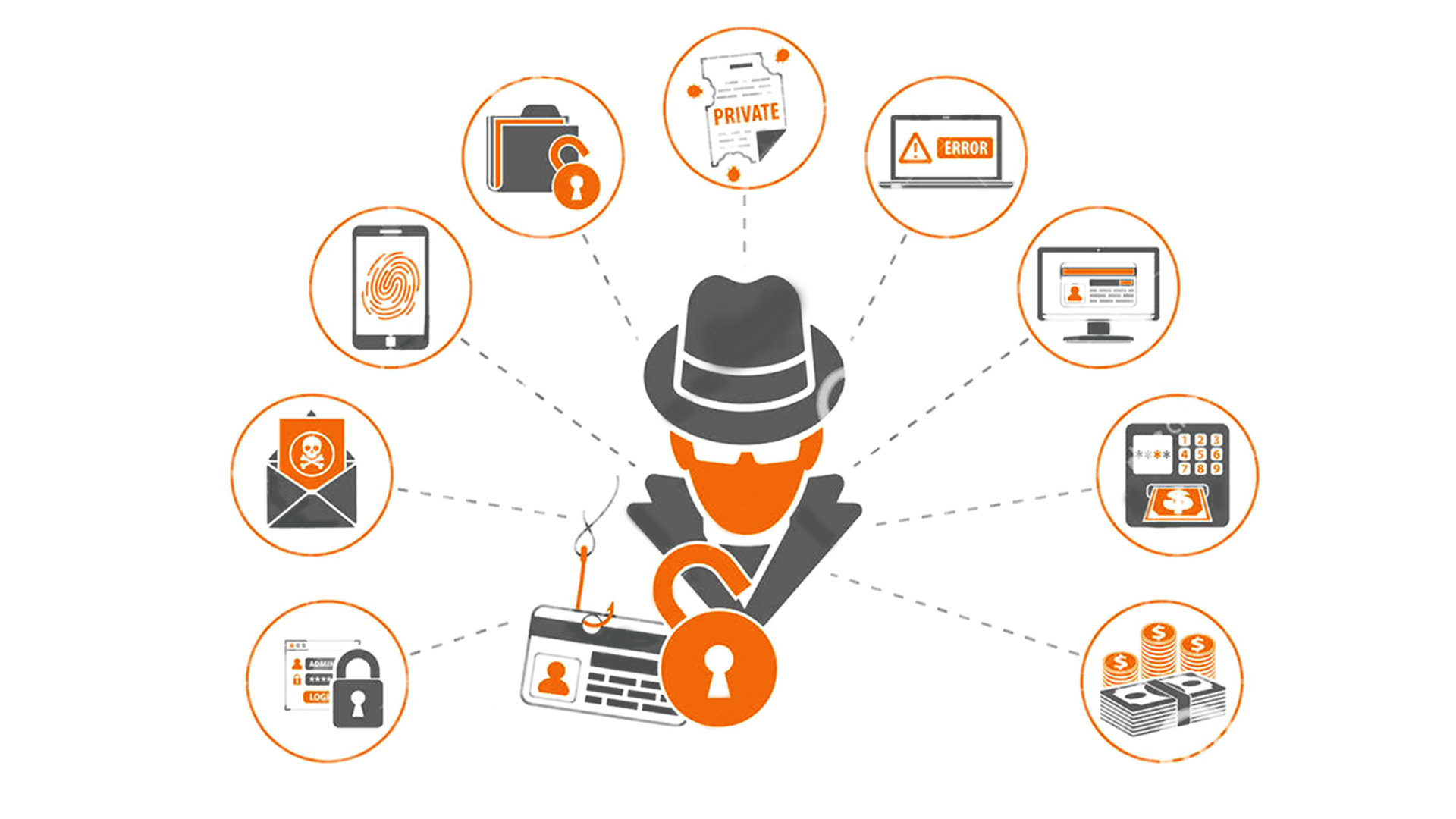
Even though you don’t realize it, your identity is all over the internet. Whether you posted to an internet forum in 1996 or you ever endured a MySpace page, these details are still out there, in addition, to protect it. There are some quick and simple ways that you can protect your digital life: 1. […]