What is Penetration Testing?
By Prempal Singh
What is Penetration Testing?
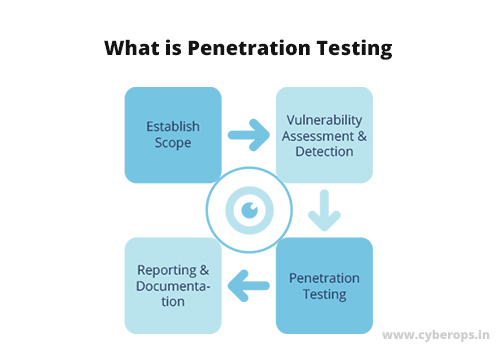
Penetration testing is one of the methods to identify areas of the system that are vulnerable to intrusion and compromise integrity and reliability from unauthorized and malicious users or entities. The penetration testing process includes deliberate authorized attacks on the system, able to identify both its weakest areas and security gaps from third-party intrusions, and thereby improve security attributes.
This technique can also be used as a supplement to other verification methods for assessing the effectiveness of the system’s protection against various types of unexpected malicious attacks.
What are the causes of system vulnerabilities?
Gaps in security appear at different stages of the process and depend on many factors:
- design error (for example, design flaws – one of the most important factors in the emergence of loopholes in security);
- Incorrect configuration and unsuccessful configuration of related hardware and software;
- network connectivity problems (secure connectivity eliminates the possibility of malicious attacks, and an unsecured network provides a gateway to hackers to attack the system);
- a human error (an error committed intentionally or unintentionally by an individual or team when designing, deploying, and maintaining a system or network);
- error of communication (incorrect or open transfer of confidential data and information to teams or individuals);
- excessive complexity of the system (it is easy to control the security mechanism of a simple network infrastructure, and it is difficult to monitor leaks or any malicious activity in complex systems);
- Insufficiency of training (lack of knowledge and proper training on security issues both among internal employees and those who work outside the organizational structure).
What is the difference between penetration testing and vulnerability assessment?
Both of these techniques pursue one goal – to make the software product safe, but have different workflows.
Penetration testing is a real-time check manually or using automation tools; the system and its associated component are exposed to simulated malicious attacks to identify security flaws.
Vulnerability assessment involves examining and analyzing the system using testing tools to detect security loopholes for several variants of malicious attacks. This technique identifies vulnerable areas that can give hackers the ability to compromise the system. In addition, in the vulnerability assessment process, various corrective measures are provided to address the identified shortcomings.
Vulnerability assessment follows a predetermined and established procedure, while penetration testing solves the only task – the destruction of the system, regardless of the approaches adopted.
What is the purpose of penetration testing?
As mentioned earlier, security gaps provide an unauthorized user or an illegal object with the ability to attack a system that affects its integrity and confidentiality. Thus, testing software for penetration helps to get rid of these vulnerabilities and make the system competent enough to protect against expected and even unexpected malicious threats and attacks.
Let us consider the results of applying this technique in more detail. So, penetration testing provides:
A way to identify weak and vulnerable areas of the system before they are noticed by a hacker. Frequent and complex system updates can affect the relevant hardware and software, which leads to security problems – hence, it is appropriate to monitor all these updates.
The possibility of assessing the existing system security mechanism. This allows developers to assess their competence to protect and maintain the level of security standards installed in the system. In addition to the vulnerability of the system, it is also recommended that business and technical teams evaluate various business risks and problems, including any compromise with the authorized and confidential data of the organization. This helps the organization to structure and prioritize, mitigating or completely eliminating various business risks and problems.
Finally (but not least), a tool for identifying and meeting certain basic standards, norms and safety practices.
How do I perform penetration testing?
The penetration testing of the system can be carried out using any of the following approaches:
- manual testing;
- automatic testing;
a combination of manual and automatic testing.
1. Manual penetration testing
To perform manual testing for the penetration of the software product, a consistent standard approach is used, including the following steps:
Planning for penetration testing. This stage includes the collection of requirements, definition of the scope, strategies and objectives of penetration testing in accordance with safety standards. In addition, it can contain an assessment and enumeration of the audited areas, types of planned tests and other related checks.
Intelligence service. Collection and analysis of the most detailed information about the system and associated security attributes, useful for targeting and attacking each block, for effective and efficient testing of the system of penetration into the system. There are two forms of collecting and analyzing information about the target system: passive and active reconnaissance (in the first case, direct interaction with the system is not supposed).
Vulnerability analysis. At this point, the tester identifies and detects vulnerable areas of the system that will be used to enter and attack using penetration tests.
Exploitation. The actual test for penetration into the system, including internal and external attacks. External attacks are emulated attacks from the outside world that prevail outside the system / network boundary (for example, gaining unauthorized access to functions and system data related to applications and servers facing the public). Internal attacks begin after the intrusion of authorized objects into the system or network and have the purpose of various actions (when compromise is achieved with integrity and truthfulness of the system) that are capable of deliberately or inadvertently compromising the system.
Post-operation. The next step is to analyze each attack on the system to assess its purpose and objectives, as well as its potential impact on system and business processes.
Reporting. In fact, the reporting includes documentary work on the activities carried out at all these stages. In addition, it can describe various risks, identified problems, vulnerable areas (used or not) and proposed to address the shortcomings of the solution.
2. Automatic penetration testing
This useful and effective approach to penetration testing involves the use of specialized tools. Automatic testing is reliable, convenient, it is very fast and easy to analyze. Testing tools are effective for accurately detecting security defects present in the system in a short time, and also for creating “crystal clear” reports.
Let’s name just a few of the popular and widely used penetration testing tools:
Nmap
Nessus
Metasploit
Wireshark
OpenSSL
Cain & Abel
THC Hydra
w3af
Many tools for automated testing can be found in the finished Linux builds ( Kali Linux , Mantra OS ).
To work on a specific project, you will have to choose a tool that meets a number of requirements and criteria:
ease of deployment, use and maintenance;
providing a simple and quick scan of the system;
the ability to automate the process of checking for identified vulnerabilities;
the availability of checking for previously detected vulnerabilities;
the ability to create simple and detailed vulnerability reports.
3. Combination of manual and automatic penetration testing
This approach can be considered optimal, as it combines the advantages of the first two options and provides operational control through reliable and accurate penetration into the software product.
Types of penetration tests
Penetration testing, depending on the elements and objects used, can be assigned to the following types:
Social engineering. Testing with the connection of the “human contingent”, able to clearly identify and receive confidential data and other information via the Internet or telephone (this group may include employees of the organization or any other authorized persons present in the organization’s network).
Web application. Used to detect security holes and other problems in several variants of web applications and services located on the client or server side.
Network service. Testing the penetration into the network to detect and detect the possibility of access to hackers or any unauthorized object.
Client part. As the name implies, this test is used to test the applications installed on the client site / application.
Remote connection. Testing a vpn or similar object that can provide access to the connected system.
Wireless network. The test is designed for wireless applications and services, including their various components and functions (routers, filter packets, encryption, decryption, etc.).
Classify testing for penetration is also possible and based on the approaches used for testing:
White box. With this approach, the tester will have full access to deep knowledge about the functioning and main attributes of the system. This testing is very effective, since understanding each aspect of the system is very useful in carrying out extensive penetration tests.
Black box. Tester only provides high-level information (for example, the URL or IP address of the organization) for performing penetration testing. A specialist can feel like a hacker who knows nothing about the system / network. This is a very laborious approach, since the tester requires a considerable amount of time to study the properties and details of the system; In addition, there is a high probability of skipping part of the areas due to lack of time and information.
Gray box. The tester gets limited information (for example, knowledge of the algorithm, architecture, internal states) to simulate an external attack on the system.
Limitations of penetration testing.
Penetration testing has a number of limitations:
- lack of time and high cost of testing
- a limited amount of testing based on requirements for a given period of time (which may lead to ignoring other important areas)
- the possibility of a system failure or loss of the system in the state of failure as a result of the penetration test
- vulnerability of data (loss, corruption or damage)
Conclusion:
Hackers armed with advanced technologies with a wide range of resources and tools often easily break into a system or network with the intent to harm the company’s reputation and assets. Penetration testing more than other types of testing can be seen as a tool to identify various security gaps that help to nullify potential threats to the system as a whole.
